Cybersecurity isn’t something you read about anymore. It’s something you do. Or you don’t get hired.
Here’s the truth most courses won’t tell you: watching tutorials about hacking is like watching someone swim and expecting to qualify for the Olympics. Doesn’t work. Never has.
An ethical hacking course with hands-on labs changes everything because you’re not memorizing commands you’re actually breaking into systems, identifying vulnerabilities, and learning why attacks succeed or fail in real-time.
At Go Hackers Cloud, we’ve built something different. Not another video library. Not death by PowerPoint. We’re talking live environments where you launch actual attacks, watch defenses crumble, and figure out how to patch the holes before the bad guys find them. Our ethical hacking course online gives you this access from anywhere, anytime.
Why Hands-On Labs Matter in Ethical Hacking
Theory dies in the interview room.
We’ve seen it happen. Candidates show up with certificates longer than their arm, but when asked to demonstrate a simple SQL injection? Blank stares. Fumbling. Excuses.
Ethical hacking practical training solves this because it forces you into uncomfortable territory where commands fail, exploits don’t work the first time, and you have to think like both attacker and defender.
What Actually Happens in Real Labs
You’re not watching someone else hack. You’re the one typing commands that could compromise a system. You’re the one who has to troubleshoot when Metasploit throws an error. You’re building muscle memory that sticks.
When employers test your skills, you won’t freeze. You’ll execute.
Labs deliver three things textbooks can’t:
- Actual problem-solving experience under pressure
- Confidence that comes from repetition and failure
- Job-ready skills that translate to day-one productivity
This ethical hacking lab-based course approach isn’t optional anymore. It’s the baseline for getting hired in 2025.
Types of Labs Included in Ethical Hacking Course
Not all labs are created equal. Some courses give you outdated virtual machines and call it “hands-on.” That’s lazy.
Go Hackers Cloud structures labs like real attack progressions starting where you are, pushing you toward where employers need you.
Beginner Labs
Here’s where foundations get built:
- Linux command line navigation and scripting
- Network protocols and packet analysis fundamentals
- Basic vulnerability scanning with automated tools
- Password cracking techniques and hash analysis
Nothing fancy yet. Just building the foundation so intermediate labs don’t overwhelm you. If you’re completely new to this field, our guide on ethical hacking basics covers everything you need to know before starting these labs.
Intermediate Labs
Now it gets interesting:
- Web application exploitation using OWASP methodologies
- Privilege escalation across Linux and Windows systems
- Cloud misconfigurations that expose entire infrastructures
- SQL injection attacks against live databases
This is where you start thinking like an attacker. Where you see a login form and immediately wonder about injection points.
Advanced Labs
The stuff that separates professionals from amateurs:
- Full red team attack chains from reconnaissance to exfiltration
- Post-exploitation persistence and lateral movement
- Detection evasion techniques that bypass security tools
- Custom exploit development for zero-day vulnerabilities
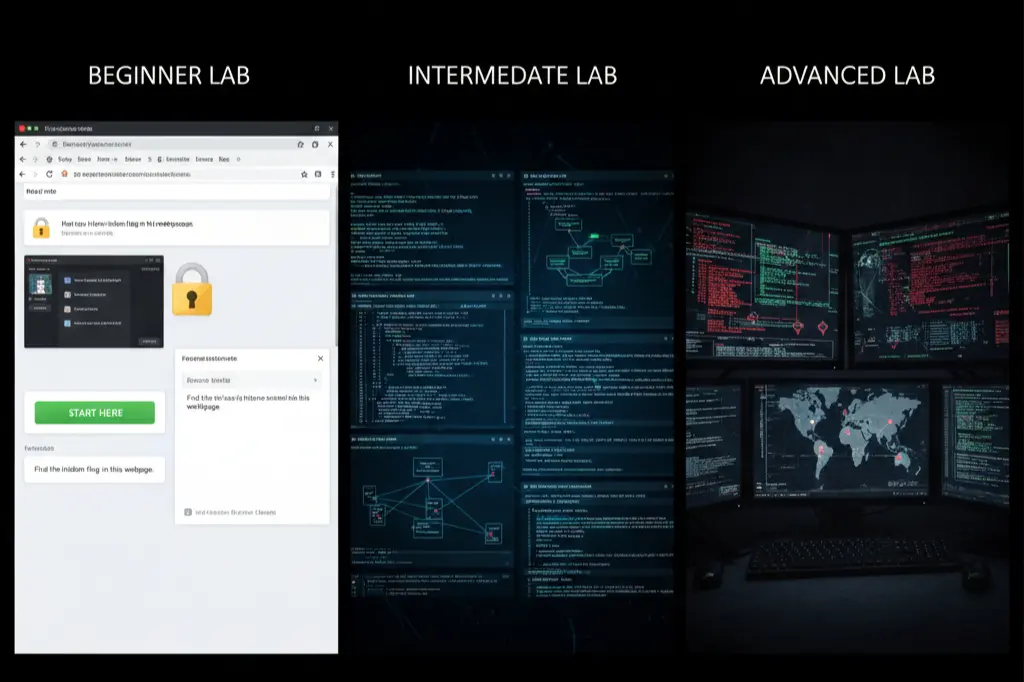
This progression mirrors how real penetration testers work. You’re not jumping into advanced exploits on day one. You’re building systematically.
That’s how real-world cybersecurity training should work.
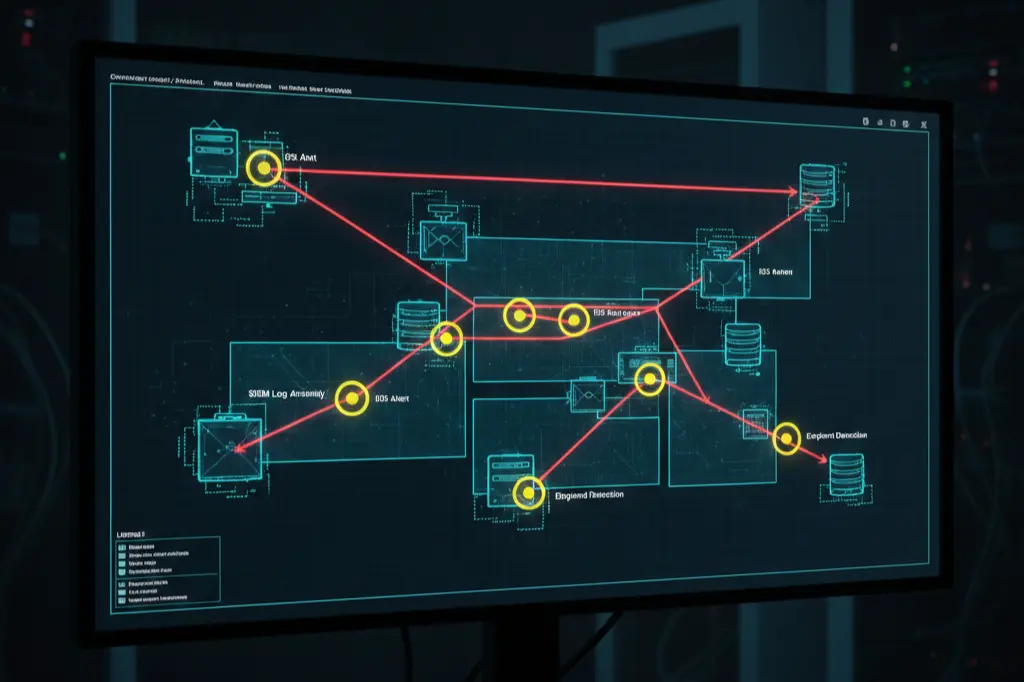
Real-World Attack & Defense Simulations
Here’s where most courses fail completely.
They teach you to attack. Period. But real cybersecurity professionals need to understand both sides how attacks work AND how defenders detect them.
Our course includes full-spectrum simulations:
- Deploying phishing campaigns and analyzing open rates
- Exploiting the OWASP Top 10 vulnerabilities in production-like environments
- Moving laterally across networks after initial compromise
- Blue team detection and incident response procedures
You learn why certain attacks get caught immediately while others go undetected for months. You discover how security information and event management (SIEM) tools flag suspicious activity. You understand the defender’s perspective.
Why This Dual Approach Matters
Because employers hire people who can:
- Test systems as an attacker
- Secure systems as a defender
- Communicate vulnerabilities to non-technical stakeholders
SOC analysts need this. Penetration testers need this. Cloud security engineers absolutely need this.
One learner told us they failed three interviews before taking our labs. After completing the simulations? Hired within two weeks. The difference? They could actually demonstrate skills during technical assessments.
Tools Practiced in Ethical Hacking Labs
Employers don’t hire based on potential anymore. They hire based on tool fluency.
This training covers the exact tools you’ll use on the job:
- Nmap for network reconnaissance and service enumeration
- Burp Suite for web application testing and proxy interception
- Metasploit for exploit development and payload delivery
- Wireshark for packet analysis and traffic inspection
- SQLmap for automated SQL injection exploitation
- Hydra for password cracking and brute force attacks
- Nikto for web server vulnerability scanning
But here’s the critical part you don’t just run these tools once and move on.
You deploy them. Break things with them. Watch them fail. Learn why exploits work against some systems but not others. Understand the defensive countermeasures that stop these tools cold.
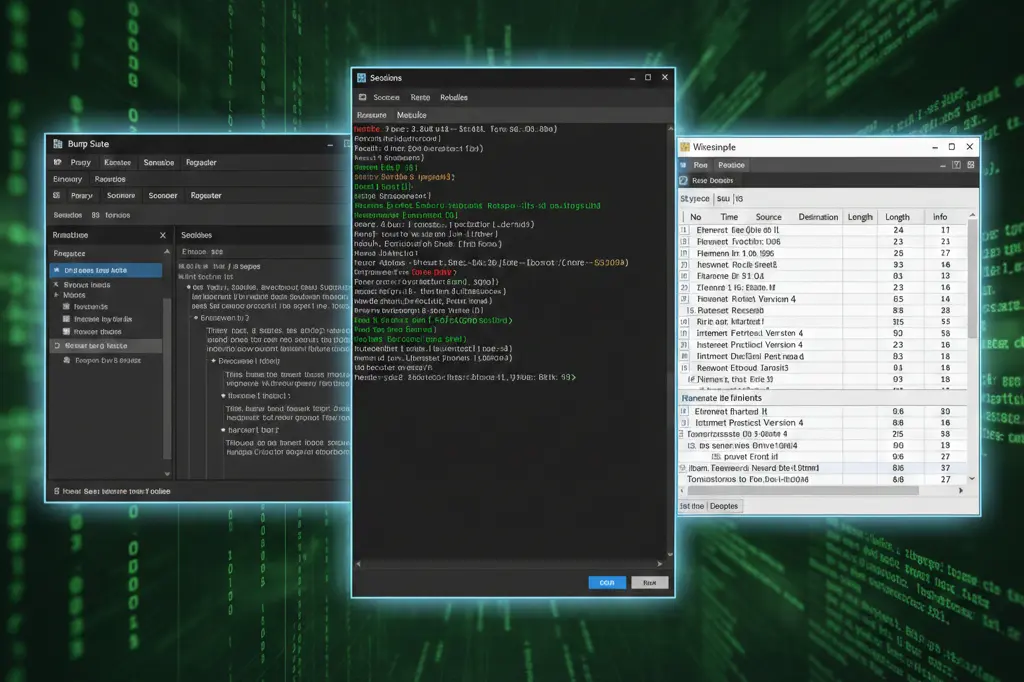
By the end of the program, you’re not “familiar” with these tools. You’re proficient. There’s a massive difference, and hiring managers spot it immediately during technical interviews.
Skill Outcomes from Lab-Based Training
Let’s get specific about what you’ll actually be able to do after completing the program.
Measurable Skills You’ll Gain
Reconnaissance & Enumeration: You’ll conduct comprehensive information gathering, identify attack surfaces, and map network topologies without triggering alarms.
Vulnerability Assessment: You’ll scan systems, interpret results, prioritize risks, and articulate findings to technical and non-technical audiences.
Exploitation Techniques: You’ll chain multiple vulnerabilities, escalate privileges, maintain persistence, and cover your tracks like a professional penetration tester.
Security Documentation: You’ll write clear, actionable reports that developers and security teams can actually use to remediate vulnerabilities.
Here’s what matters most you can demonstrate these skills practically, not just talk about them theoretically. This is what we mean by job-ready ethical hacking training that employers actually respect.
When a recruiter says “show me how you’d test this login form,” you don’t panic. You open Burp Suite and show them.
That’s the difference between lab-trained professionals and certificate collectors.
How Go Hackers Cloud Delivers Real Labs
We’re not course creators who dabbled in cybersecurity. We’re cybersecurity professionals who built a training platform because existing options were inadequate.
What Makes Our Labs Different
Cloud-Hosted Real Environments: No downloading broken virtual machines. No compatibility issues. You access fully functional attack environments through your browser, identical to what penetration testers use in actual engagements.
Isolated Attack Sandboxes: Practice without consequences. Break systems, crash services, corrupt databases all in environments designed for experimentation and learning through failure.
Guided + Unguided Practice Modes: Early labs walk you through attacks step-by-step. Advanced labs drop you into scenarios with minimal guidance, forcing you to think independently and research solutions.
Mentor-Reviewed Lab Outcomes: Submit your findings, exploitation techniques, and remediation recommendations. Get feedback from working penetration testers who’ve conducted hundreds of real-world assessments.

This lab-based learning model ensures you make mistakes safely, learn by fixing failures, and gain confidence through repetition not by reading about what might happen.
Visit https://gohackerscloud.com/ to see exactly how our lab infrastructure works. No marketing fluff. Just transparent demonstrations of what you’ll actually be doing.
Who Should Choose a Lab-Focused Ethical Hacking Course
This course works for specific people with specific goals.
Complete Beginners
You’ve heard about cybersecurity careers, read articles about six-figure salaries, and want to break into the field without a computer science degree. Lab-based learning gives you practical proof of skills that compensates for lack of formal credentials.
IT Professionals Transitioning
You’ve been a network admin, system administrator, or help desk technician for years. You understand infrastructure but need offensive security skills to make the career jump. Labs accelerate your learning because you’re not starting from zero.
Students Preparing for Certifications
CEH, OSCP, PNPT every major ethical hacking certification requires practical demonstrations. Our labs align directly with certification objectives, giving you the hands-on experience exams actually test.
Working Professionals Upskilling
Your organization needs penetration testing capabilities. You’re tasked with building security skills while maintaining your current role. Lab-based training works around your schedule with 24/7 access to environments.

If your goal involves employment, freelancing, consulting, or career advancement in cybersecurity, lab-based learning isn’t negotiable. It’s the standard employers expect in 2025.
Hands-On Ethical Hacking Training FAQ’s
Can complete beginners really learn ethical hacking through labs?
Yes. Our labs start with foundational concepts like Linux basics and networking fundamentals before progressing to advanced exploitation techniques. You’re not thrown into deep water you’re guided systematically through each skill level.
Are these actual live environments or just recorded demonstrations?
All labs are live, interactive environments hosted in the cloud. You’re executing real commands against real systems in real-time, not watching pre-recorded videos of someone else hacking.
Do I need programming knowledge before starting?
Basic scripting helps but isn’t required. The course teaches necessary coding skills as you progress, focusing on Python and Bash scripting relevant to penetration testing and automation.
Will this training help me pass certification exams like CEH or OSCP?
Absolutely. The labs align directly with certification objectives and provide the practical experience these exams test. Many learners use our platform specifically to prepare for practical certification assessments.
How realistic are the attack scenarios?
Every lab is based on real-world scenarios pulled from actual penetration testing engagements. You’re practicing attacks that organizations face daily, not theoretical exploits that don’t exist in production environments.
Can I access labs while working full-time?
Yes. Lab environments are available 24/7 with no scheduling restrictions. Work through exercises during lunch breaks, evenings, or weekends whatever fits your schedule.
Start Your Lab Access Today
Cybersecurity rewards action, not intention.
Every day you spend watching videos instead of breaking systems is another day your competition gains practical experience.
By enrolling at Go Hackers Cloud, you’re not just learning concepts you’re building verifiable proof of skills that hiring managers can test during interviews.
You reduce the on-the-job learning curve because you’ve already made mistakes in safe environments. You increase placement success because you can demonstrate competency, not just claim it.
The question isn’t whether hands-on labs matter. The question is whether you’re serious enough about cybersecurity to actually practice it.
Ready to stop learning passively and start hacking ethically?
Enroll now at https://gohackerscloud.com/ and get immediate access to live lab environments, real attack simulations, expert mentorship, and the practical skills that actually get you hired in cybersecurity. Your first penetration test starts today, not someday.


